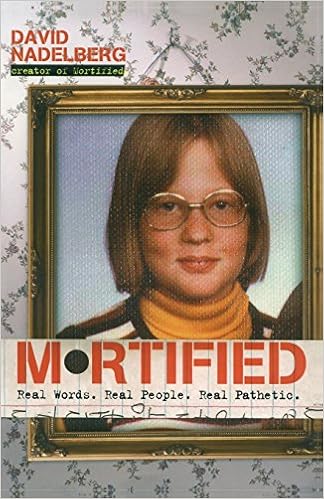
By David Nadelberg
Within the days ahead of blogs, young children recorded their lives with a pen in top-secret notebooks, often emblazoned with an earnest, underlined plea to oldsters to maintain away. in view that 2002, David Nadelberg has tapped that huge wellspring of adolescent affliction within the degree express Mortified, during which grown women and men confront their earlier with firsthand stories in their first kiss, first puff, worst promenade, fights with mother, lifestyles at bible camp, worst hand activity, top mall activity, and purposes they deserved to marry Simon LeBon.
Following a similar formulation that has made the reside convey a loved cult hit, Mortified the publication takes actual adolescence journals and records and edits the entries into beautiful, comedic, and cathartic tales, brought by way of their now older (and allegedly wiser) authors. From letters begging rescue from a hellish summer season camp to catty locker notes approximately stuck-up classmates to obsessive love that borders on stalking, Mortified provides voice to the genuine -- and very pathetic -- hopes, fears, wants, and artistic urgings that experience united children for generations.
Read or Download Mortified: Real Words. Real People. Real Pathetic. PDF
Similar nonfiction books
Written with acclaimed tune journalist Ann Powers, Tori Amos: Piece by means of Piece is a firsthand account of the main complicated and intimate information of Amos’s existence as either a personal person and a truly public appearing musician. In passionate and informative prose, Amos explains how her songs come to her and the way she files after which plays them for audiences far and wide, all of the whereas connecting with listeners internationally and conserving her family existence (which contains elevating a tender daughter).
Reverse Deception: Organized Cyber Threat Counter-Exploitation (1st Edition)
A whole consultant to figuring out and battling complicated power threats—today's so much damaging chance to firm security
Reverse Deception: equipped Cyber hazard Counter-Exploitation explains find out how to establish complicated power threats (APTs), categorize them based on danger point, and prioritize your activities as a result via employing professional, field-tested deepest- and government-sector equipment (NSA, FBI, and DOD).
APTs can't be noticeable, unfold invisibly, after which proceed to stay in an company community, undetected. during this specific booklet, the authors clarify how you can get—and stay—ahead of today's well-organized and very power model of community enemies. The publication describes the features of malware and botnets, how they could morph, sidestep detection, and spin off decoys that dwell in-network, whereas showing to were wiped clean up and debugged. This exact advisor then unearths how one can become aware of the looks of malicious code, decode the kinds of enemies they originate from, and eventually, tips on how to extricate malcode and deflect its destiny access into networks.
Reverse Deception: equipped Cyber danger Counter-Exploitation features:
> complete insurance of the number 1 feared kind of community assault at the present time, the APT
> Descriptions of cyber espionage strategies noticeable within the U. S. and the world over, with comparisons of the categories of countermeasures permissible through legislations within the U. S. and Asia as opposed to much less strict international locations in Europe, the center East, and Africa
> mesmerizing case stories and precise tales from the authors' FBI, DOD, NSA, and personal quarter work
> Foreword by means of Fred Feer, a safety expert with forty years' event with the U. S. military counterintelligence, CIA, RAND, and autonomous consulting
> whole assurance of key points of deception, counter-deception, behavioral profiling, and protection in the cyber realm
> Cat-and-mouse suggestions from the easiest within the game—explains easy methods to enforce deception and disinformation options opposed to a number of incoming threats aimed toward attractive adversaries out into the open
> A clean point of view on leading edge, field-tested principles for effectively countering present electronic threats—plus anticipated features of the subsequent threats to come
> felony reasons of features, barriers, and specifications for aiding legislation enforcement investigations
Coverage includes:
Deception all through background to this day; The purposes & pursuits of Cyber Counterintelligence; The Missions and results of legal Profiling; felony & moral points of Deception; assault Tradecraft; Operational Deception; instruments, strategies & systems; assault Attribution; Black Hat Motivators; figuring out complicated continual Threats; whilst & whilst to not Act; Implementation & Validation strategies
“Each of those little books is witty and dramatic and creates a feeling of time, position, and personality. .. .I can't ponder a greater method to introduce oneself and one’s neighbors to Western civilization. ”—Katherine A. Powers, Boston Globe. “Well-written, transparent and expert, they've got a breezy wit approximately them.
Translated via John & Charlotte Stanley.
With a Foreword through Robert A. Nisbet & an creation by means of Joh Stanley
It is a excitement to welcome this booklet into the English language, the extra so for the final excellence of the interpretation and for the precious advent that Professor Stanley has given to Sorel's paintings. This Frenchman has been in a position to reveal to the very center the trendy thought of growth, the concept that mankind has improved in linear type some time past, is now progressing, and should proceed to growth indefinitely into the long run, got here into being within the French Enlightenment.
- OS X 10.8 Mountain Lion: the Ars Technica Review
- The Stock Option Income Generator: How To Make Steady Profits by Renting Your Stocks (Wiley Trading)
- The Reef Aquarium, Volume 2: A Comprehensive Guide to the Identification and Care of Tropical Marine Invertebrates
- Revive: Stop Feeling Spent and Start Living Again
Extra resources for Mortified: Real Words. Real People. Real Pathetic.
Sample text
Neil’s sensitivity to this force is often expressed somewhat bitterly, in small signs of resentment that occasionally appear amid the seeming idyll of budding romance. When Brenda vaguely indicates that she goes to college in Boston, Neil tells the reader, testily, that he’s not embarrassed to tell people he attended Newark Colleges of Rutgers (GC 10). When Brenda casually mentions that she “lived in Newark when [she] was a baby,” Neil is suddenly, unaccountably, angry (GC 12). And when Brenda unwittingly derides Newark in chastising her mother for not properly adapting to the family’s affluence, Neil cannot “shake from [his] elephant’s brain that she-still-thinks-we-live-in-Newark remark” (GC 24).
In this way, Neil’s sometimes ardent, often conflicted love affair with Brenda is also a love affair with Short Hills, with the increasingly prosperous lifestyle of American Jews. Near the end of the novella, when Neil is apprehensive about his future with Brenda, he wanders into a cathedral and informally addresses God. What is he after? What is he pursuing? Which prize will be his reward? “Which prize do you think, schmuck? Gold dinnerware, sporting-goods trees, The American Jewish Experience and the New York Intellectuals 27 nectarines, garbage disposals, bumpless noses, Patimkin Sink, Bonwit Teller—” (GC 92).
The Patimkins are a nouveau riche Jewish family living in Short Hills, a prosperous New Jersey suburb less than ten miles away from Newark on the map, but much further in terms of lifestyle. Early in the story, Neil asks his aunt where she keeps the suburban phone book, so he can call Brenda. Aunt Gladys is typically exasperated: “That skinny book? ” (GC 4). Later, Aunt Gladys, ever the voice of urban Jewishness, asks, “Since when do Jewish people live in Short Hills? They couldn’t be real Jews believe me” (GC 53).



