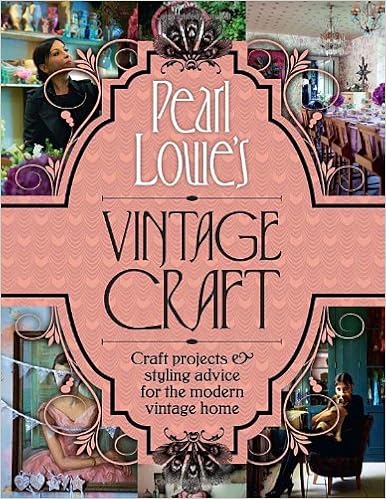
By Pearl Lowe
Classic fashion designer Pearl Lowe exhibits you ways to create the real classic glance on your own residence along with her specialist suggestion and straightforward craft tasks. This functional advisor, entire with inspiring images comprises ...* 50 step by step craft tasks * stitching, portray, upcycling and crafting secrets and techniques * A how-to consultant to sourcing your individual classic treasures * And Pearl's little black booklet of outlets and providers An absolute must-have for fans of classic and all issues hand-crafted. Craft tasks contain ...Dyed lace window panels classic bunting Midsummer and iciness wreaths Gypsy-style apron Two-toned fringed lampshade customized rubber stamp luxurious padded headboard Upcycled chest of attracts old ghost reflect hand-crafted vintage-style tiles
Read or Download Pearl Lowe's Vintage Craft: 50 Craft Projects and Home Styling Advice PDF
Best nonfiction books
Written with acclaimed tune journalist Ann Powers, Tori Amos: Piece by means of Piece is a firsthand account of the main difficult and intimate information of Amos’s lifestyles as either a personal person and a truly public appearing musician. In passionate and informative prose, Amos explains how her songs come to her and the way she files after which plays them for audiences all over, the entire whereas connecting with listeners the world over and keeping her circle of relatives lifestyles (which comprises elevating a tender daughter).
Reverse Deception: Organized Cyber Threat Counter-Exploitation (1st Edition)
An entire advisor to figuring out and scuffling with complicated power threats—today's such a lot harmful danger to firm security
Reverse Deception: geared up Cyber probability Counter-Exploitation explains tips to determine complex power threats (APTs), categorize them in line with hazard point, and prioritize your activities consequently by means of employing professional, field-tested deepest- and government-sector tools (NSA, FBI, and DOD).
APTs can't be noticeable, unfold invisibly, after which proceed to dwell in an company community, undetected. during this exclusive booklet, the authors clarify tips to get—and stay—ahead of today's well-organized and intensely power model of community enemies. The publication describes the features of malware and botnets, how they could morph, keep away from detection, and spin off decoys that reside in-network, whereas showing to were wiped clean up and debugged. This certain advisor then finds how you can become aware of the looks of malicious code, decode the kinds of enemies they originate from, and eventually, find out how to extricate malcode and deflect its destiny access into networks.
Reverse Deception: equipped Cyber hazard Counter-Exploitation features:
> complete assurance of the number one feared form of community assault this present day, the APT
> Descriptions of cyber espionage strategies visible within the U. S. and across the world, with comparisons of the kinds of countermeasures permissible through legislation within the U. S. and Asia as opposed to much less strict nations in Europe, the center East, and Africa
> mesmerizing case reviews and actual tales from the authors' FBI, DOD, NSA, and personal zone work
> Foreword by means of Fred Feer, a safety specialist with forty years' adventure with the U. S. military counterintelligence, CIA, RAND, and autonomous consulting
> whole insurance of key features of deception, counter-deception, behavioral profiling, and safety in the cyber realm
> Cat-and-mouse options from the easiest within the game—explains the right way to enforce deception and disinformation innovations opposed to quite a few incoming threats geared toward engaging adversaries out into the open
> A clean standpoint on leading edge, field-tested rules for effectively countering present electronic threats—plus anticipated features of the subsequent threats to come
> felony reasons of services, barriers, and necessities for helping legislations enforcement investigations
Coverage includes:
Deception all through background to this present day; The purposes & objectives of Cyber Counterintelligence; The Missions and results of felony Profiling; criminal & moral points of Deception; assault Tradecraft; Operational Deception; instruments, strategies & approaches; assault Attribution; Black Hat Motivators; figuring out complex power Threats; while & whilst to not Act; Implementation & Validation strategies
“Each of those little books is witty and dramatic and creates a feeling of time, position, and personality. .. .I can't consider a greater method to introduce oneself and one’s associates to Western civilization. ”—Katherine A. Powers, Boston Globe. “Well-written, transparent and knowledgeable, they've got a breezy wit approximately them.
Translated through John & Charlotte Stanley.
With a Foreword through Robert A. Nisbet & an creation through Joh Stanley
It is a excitement to welcome this ebook into the English language, the extra so for the overall excellence of the interpretation and for the dear advent that Professor Stanley has given to Sorel's paintings. This Frenchman has been in a position to divulge to the very center the fashionable notion of growth, the concept mankind has stepped forward in linear model long ago, is now progressing, and may proceed to development indefinitely into the long run, got here into being within the French Enlightenment.
- The Last Rhinos: My Battle to Save One of the World's Greatest Creatures
- Computer Graphics, C Version (2nd Edition)
- Specimens of the table talk of the late Samuel Taylor Coleridge.
- Sonic Experience: A Guide To Everyday Sounds
- One-Block Wonders: One Fabric, One Shape, One-of-a-kind Quilts
- WebGL Hotshot
Extra resources for Pearl Lowe's Vintage Craft: 50 Craft Projects and Home Styling Advice
Example text
To explore them to grasp not just the most recent forms of activism! but its broad ethical basis. Non-violent protest has a number of traditions and a long history. In such actions as boycotts and strikes, we can find non-violent protests far back in history. It is not hard to understand this long lineage. Non-violent protests based on withdrawing co-operation both strike at the heart of society and sidestep any superior force the target might have. Workers’ strikes operate with such principles.
The Zapatista attack on neo-liberalism has had wide resonance and been part of a shift within some green movements to participation in anti-neo-liberal globalization protests. Yet it remains the case that what might be transgressive for one movement, may not be for another. The social system or institution that must be made anew for one movement may be a vehicle for change for others. For example, some argue that legal systems must be transgressed because they presume private property as a given, and private property is inherently exploitative.
This leads, Gandhi believed, to the oppressor realizing their own moral and spiritual failures and then giving way. Second, practitioners build their own spiritual position, because non-violence leads to truth. The goodness and morality of followers of satyagraha is constantly developed and demonstrated by practising satyagraha. Simultaneous with such metaphysical concerns is the act of non-violence – boycott, refusal to co-operate and so on – that provides practical teeth for satyagraha’s high ideals.



