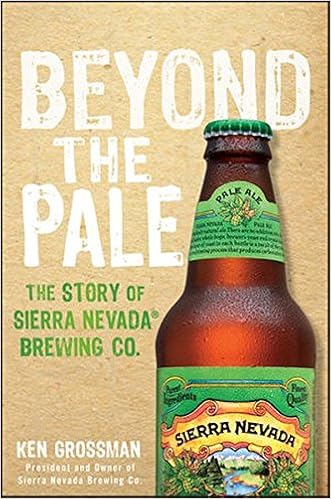
By Ken Grossman
Personal stories of perseverance and beer making from the founding father of Sierra Nevada Brewing Co.
Beyond the Pale chronicles Ken Grossman's trip from hobbyist homebrewer to proprietor of Sierra Nevada Brewing Co., some of the most winning craft breweries within the usa. From younger adventures to pioneering craft brewer, Ken Grossman stocks the rigors and tribulations of establishing a brewery that produces greater than 800,000 barrels of beer a yr whereas keeping its dedication to utilizing the best materials to be had. seeing that Grossman based Sierra Nevada in 1980, a part of a becoming beer revolution in the US, critics have proclaimed his beer to be "among the easiest brewed at any place within the world."
• Beyond the Pale describes Grossman's new angle to creating and allotting one in every of America's best-loved manufacturers of beer, whereas targeting humans, the planet and the product
• Explores the "Sierra Nevada way," as exemplified through founder Ken Grossman, such as an emphasis on sustainability, nonconformity, following one's ardour, and doing issues the appropriate way
• information Grossman's begin, home-brewing five-gallon batches of beer on his personal, turning into a informed domestic brewer, and later, development a small brewery within the city of Chico, California
Beyond the Pale indicates how with exertions, commitment, and concentration, you will be winning following your dream.
Read or Download Beyond the Pale: The Story of Sierra Nevada Brewing Co. PDF
Best nonfiction books
Written with acclaimed song journalist Ann Powers, Tori Amos: Piece via Piece is a firsthand account of the main elaborate and intimate information of Amos’s existence as either a personal person and a really public appearing musician. In passionate and informative prose, Amos explains how her songs come to her and the way she documents after which plays them for audiences in every single place, all of the whereas connecting with listeners internationally and conserving her circle of relatives lifestyles (which comprises elevating a tender daughter).
Reverse Deception: Organized Cyber Threat Counter-Exploitation (1st Edition)
An entire advisor to realizing and combating complex power threats—today's such a lot damaging danger to company security
Reverse Deception: prepared Cyber risk Counter-Exploitation explains tips to establish complex power threats (APTs), categorize them in accordance with threat point, and prioritize your activities hence by way of making use of professional, field-tested inner most- and government-sector equipment (NSA, FBI, and DOD).
APTs can't be noticeable, unfold invisibly, after which proceed to reside in an firm community, undetected. during this different publication, the authors clarify the right way to get—and stay—ahead of today's well-organized and very chronic model of community enemies. The booklet describes the features of malware and botnets, how they could morph, circumvent detection, and spin off decoys that stay in-network, whereas showing to were wiped clean up and debugged. This designated advisor then unearths tips on how to notice the looks of malicious code, decode the categories of enemies they originate from, and eventually, the way to extricate malcode and deflect its destiny access into networks.
Reverse Deception: prepared Cyber hazard Counter-Exploitation features:
> complete assurance of the number 1 feared form of community assault this day, the APT
> Descriptions of cyber espionage strategies visible within the U. S. and across the world, with comparisons of the categories of countermeasures permissible by means of legislations within the U. S. and Asia as opposed to much less strict nations in Europe, the center East, and Africa
> spell binding case experiences and precise tales from the authors' FBI, DOD, NSA, and personal region work
> Foreword via Fred Feer, a safety expert with forty years' adventure with the U. S. military counterintelligence, CIA, RAND, and autonomous consulting
> whole insurance of key features of deception, counter-deception, behavioral profiling, and safeguard in the cyber realm
> Cat-and-mouse thoughts from the simplest within the game—explains easy methods to enforce deception and disinformation thoughts opposed to a number of incoming threats geared toward engaging adversaries out into the open
> A clean point of view on leading edge, field-tested principles for effectively countering present electronic threats—plus anticipated features of the following threats to come
> felony reasons of features, barriers, and requisites for aiding legislation enforcement investigations
Coverage includes:
Deception all through heritage to at the present time; The functions & targets of Cyber Counterintelligence; The Missions and results of felony Profiling; criminal & moral points of Deception; assault Tradecraft; Operational Deception; instruments, strategies & techniques; assault Attribution; Black Hat Motivators; figuring out complicated chronic Threats; whilst & while to not Act; Implementation & Validation strategies
“Each of those little books is witty and dramatic and creates a feeling of time, position, and personality. .. .I can't ponder a greater approach to introduce oneself and one’s neighbors to Western civilization. ”—Katherine A. Powers, Boston Globe. “Well-written, transparent and expert, they've got a breezy wit approximately them.
Translated by way of John & Charlotte Stanley.
With a Foreword by means of Robert A. Nisbet & an advent through Joh Stanley
It is a excitement to welcome this publication into the English language, the extra so for the overall excellence of the interpretation and for the precious creation that Professor Stanley has given to Sorel's paintings. This Frenchman has been in a position to reveal to the very middle the trendy suggestion of development, the concept that mankind has improved in linear type long ago, is now progressing, and should proceed to growth indefinitely into the longer term, got here into being within the French Enlightenment.
- The Guns of August
- A Manager's Guide to ISO22301
- Lost in Mongolia: Rafting the World's Last Unchallenged River
- Beyond Blood Identities: Posthumanity in the Twenty-First Century
Extra resources for Beyond the Pale: The Story of Sierra Nevada Brewing Co.
Sample text
Then she visited in high style, along with her new husband and his show featuring nude portraits he painted of her. What a life for an exhibitionist! ) Yet the sexual content of explicit art is said to be acceptable because the artist has alchemically transmuted base material into capital-A Art; and the runway’s ever-shifting array of alluring, skimpy, sexually suggestive clothing can be purchased for Fashion’s sake, not to send an erotic message or get a thrill. Many a voyeur has been confused by a sexy package of clothing containing a very sex-negative person!
You may want to describe porn scenarios to your partner later, or use them for a fantasy jumping-off place. “Hot talk” audio may also interest you, as may expert phone fantasy professionals. One-on-one chat lines provide a good forum for the écouteur, but the person on the other end will probably expect you to talk back. If you just want to listen, you might look for a party line where a number of people call in for a sort of telephone orgy. A sharp-eared wallflower at a “gathering” like this can learn a lot.
You may want to restrict your viewing, at least at first, to certain porn genres – lesbian, all-male, women-made, or those featuring types of sex you particularly love. In this culture, where sexual curiosity too often mutates into sexual shame, we often find our first exposure to porn uncomfortable or shocking. After all, we know it’s supposed to be dirty. We haven’t had the opportunity to get used to the sight of people fucking right in front of us! Over time, though, those shameful feelings can fade – unless, of course, we’ve incorporated them into what we like about porn.



