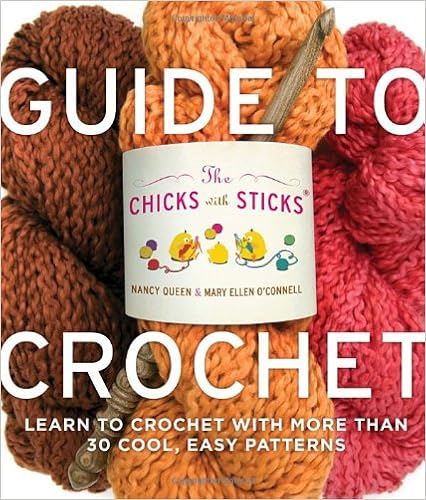
By Nancy Queen, Mary Ellen O'Connell
Sign up for the clique of the Chicks with Sticks!
Anyone can do it. an individual. cease pondering. cease being afraid. cease sweating, you’ll get the hook all damp. sure, with assistance from the Chicks with Sticks, an individual can learn how to crochet in precisely a weekend—and via Sunday evening, novices will comprehend what they’re doing and feature the arrogance to do it. complex rookies (the ones who've already made an afghan sq.) could have clean, fashion-forward initiatives to put on round city. First up is an introductory part on instruments and fabrics. Then the Chicks current a sequence of classes that every introduce a brand new ability and styles that support readers study and grasp it earlier than relocating on. The greater than 30 tasks diversity from cool belts to lovely scarves, from felted baggage to sophisticated wraps and sweaters. all through, the Chicks with Sticks are status by means of with quips and anecdotes, help and sisterhood. studying to crochet hasn't ever been so enjoyable . . . and so empowering!
Read or Download The Chicks with Sticks Guide to Crochet: Learn to Crochet with more than 30 Cool, Easy Patterns PDF
Similar nonfiction books
Written with acclaimed song journalist Ann Powers, Tori Amos: Piece by means of Piece is a firsthand account of the main problematic and intimate information of Amos’s lifestyles as either a personal person and a truly public appearing musician. In passionate and informative prose, Amos explains how her songs come to her and the way she files after which plays them for audiences in all places, all of the whereas connecting with listeners internationally and keeping her family existence (which contains elevating a tender daughter).
Reverse Deception: Organized Cyber Threat Counter-Exploitation (1st Edition)
An entire advisor to figuring out and scuffling with complicated chronic threats—today's such a lot harmful chance to company security
Reverse Deception: equipped Cyber probability Counter-Exploitation explains the best way to establish complicated chronic threats (APTs), categorize them in line with danger point, and prioritize your activities for this reason via making use of professional, field-tested deepest- and government-sector tools (NSA, FBI, and DOD).
APTs can't be obvious, unfold invisibly, after which proceed to stay in an company community, undetected. during this special e-book, the authors clarify how one can get—and stay—ahead of today's well-organized and very continual model of community enemies. The publication describes the features of malware and botnets, how they could morph, stay clear of detection, and spin off decoys that dwell in-network, whereas showing to were wiped clean up and debugged. This special advisor then finds how you can notice the looks of malicious code, decode the kinds of enemies they originate from, and at last, easy methods to extricate malcode and deflect its destiny access into networks.
Reverse Deception: equipped Cyber hazard Counter-Exploitation features:
> complete insurance of the number one feared form of community assault this present day, the APT
> Descriptions of cyber espionage strategies visible within the U. S. and the world over, with comparisons of the categories of countermeasures permissible through legislations within the U. S. and Asia as opposed to much less strict international locations in Europe, the center East, and Africa
> mesmerizing case reports and precise tales from the authors' FBI, DOD, NSA, and personal zone work
> Foreword via Fred Feer, a safety expert with forty years' event with the U. S. military counterintelligence, CIA, RAND, and self sustaining consulting
> whole assurance of key features of deception, counter-deception, behavioral profiling, and safeguard in the cyber realm
> Cat-and-mouse options from the simplest within the game—explains tips on how to enforce deception and disinformation innovations opposed to various incoming threats geared toward engaging adversaries out into the open
> A clean point of view on cutting edge, field-tested principles for effectively countering present electronic threats—plus anticipated features of the subsequent threats to come
> felony reasons of features, obstacles, and specifications for aiding legislation enforcement investigations
Coverage includes:
Deception all through background to at the present time; The functions & pursuits of Cyber Counterintelligence; The Missions and results of felony Profiling; felony & moral elements of Deception; assault Tradecraft; Operational Deception; instruments, strategies & tactics; assault Attribution; Black Hat Motivators; knowing complex chronic Threats; whilst & while to not Act; Implementation & Validation strategies
“Each of those little books is witty and dramatic and creates a feeling of time, position, and personality. .. .I can't examine a greater option to introduce oneself and one’s buddies to Western civilization. ”—Katherine A. Powers, Boston Globe. “Well-written, transparent and educated, they've got a breezy wit approximately them.
Translated via John & Charlotte Stanley.
With a Foreword via Robert A. Nisbet & an creation by way of Joh Stanley
It is a excitement to welcome this e-book into the English language, the extra so for the overall excellence of the interpretation and for the dear advent that Professor Stanley has given to Sorel's paintings. This Frenchman has been in a position to divulge to the very center the fashionable proposal of growth, the concept mankind has stepped forward in linear type long ago, is now progressing, and may proceed to development indefinitely into the longer term, got here into being within the French Enlightenment.
- Behind the Dolphin Smile: One Man's Campaign to Protect the World's Dolphins
- Core Auditing Standards for Practitioners
- The Myth of the Muslim Tide: Do Immigrants Threaten the West?
- Beginning Shell Scripting (Programmer to Programmer)
Additional resources for The Chicks with Sticks Guide to Crochet: Learn to Crochet with more than 30 Cool, Easy Patterns
Sample text
For many years his body was gibbeted downstream, at Tilbury. His memory survives principally in that his ‘treasure’, if treasure there be, has never been found. com PHOTOS: © CLASSIC IMAGE/ALAMY/HOBERMAN COLLECTION/TOPHAM/PRESSASSOCIATION/DEREK BAYES/LEBRECHT MUSIC & A/PICTORIAL PRESS LTD/CORBIS The Prospect of Whitby claims to be London’s oldest riverside pub. Dating from 1520, it was originally known as the Devil’s Tavern – doubtless reflective of the clientele it attracted. Patrons of a more reputable disposition included Dickens, Pepys, and the artists Whistler and Turner.
Visitors don’t have access to the room behind the balcony – it’s still very much the private part of the palace where the Queen has her apartments. But, every summer since 1993, 400,000 visitors get to marvel at the state rooms of the West Wing, view some of the palace’s 20,000 works of art on display, and walk in the footsteps of the great and the good – from Sir Winston Churchill to Nelson Mandela, and Laurence Olivier to Dame Judi Dench. Beyond the covered carriage entrance, the impact of the Many of the 775 rooms of Buckingham Palace are offices for a staff that swells up to 900 in the summer months Grand Hall is somewhat muted compared to what comes next.
This part of the riverside was one of London’s worst slums. For Dickens it was Jacob’s Island, where Bill Sikes, arch criminal of Oliver Twist met his death. ” It made Wapping sound positively salubrious, The Docklands Facing page, top: Judge Jeffreys is captured despite his disguise. Bottom: Jeffreys watched hangings from The Angel This page, clockwise from top: Enclosed docks began to restrict smuggling; postwar the East End improved for families; The Railway Tavern in Limehouse was a popular dockers' pub STEP INTO SMUGGLERS' SHOES • Sailortown, at the Museum of London Docklands, is a full-size, walk-through reconstruction of 19th-century maritime Wapping – complete with alehouse, chandlery and other buildings.



