By Paul Hoffman
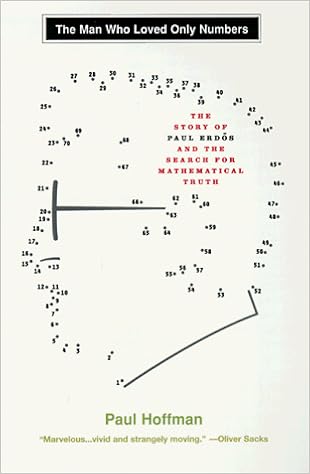
The biography of a mathematical genius. Paul Erdos used to be the main prolific natural mathematician in background and, arguably, the strangest too. 'A mathematical genius of the 1st order, Paul Erdos was once absolutely enthusiastic about his topic - he concept and wrote arithmetic for nineteen hours an afternoon until eventually he died. He travelled regularly, residing out of a plastic bag and had no real interest in meals, intercourse, companionship, artwork - all that's frequently indispensible to a human existence. Paul Hoffman, during this marvellous biography, provides us a shiny and unusually relocating portrait of this singular creature, person who brings out not just Erdos's genius and his oddness, yet his heat and experience of enjoyable, the joyfulness of his unusual life.' Oliver Sacks for 6 many years Erdos had no task, no leisure pursuits, no spouse, no domestic; he by no means learnt to cook dinner, do laundry, force a automobile and died a virgin. in its place he travelled the realm along with his mom in tow, arriving on the doorstep of esteemed mathematicians stating 'My mind is open'. He travelled until eventually his loss of life at eighty three, racing throughout 4 continents to end up as many theorems as attainable, fuelled by means of a nutrition of coffee and amphetamines. With greater than 1,500 papers written or co-written, a regular regimen of nineteen hours of arithmetic an afternoon, seven days per week, Paul Erdos used to be probably the most impressive thinkers of our occasions.
Read or Download The Man Who Loved Only Numbers: The Story of Paul Erdos and the Search for Mathematical Truth PDF
Similar nonfiction books
Written with acclaimed song journalist Ann Powers, Tori Amos: Piece through Piece is a firsthand account of the main elaborate and intimate information of Amos’s lifestyles as either a personal person and a truly public acting musician. In passionate and informative prose, Amos explains how her songs come to her and the way she documents after which plays them for audiences in all places, all of the whereas connecting with listeners internationally and preserving her family existence (which contains elevating a tender daughter).
Reverse Deception: Organized Cyber Threat Counter-Exploitation (1st Edition)
A whole consultant to knowing and struggling with complex power threats—today's so much harmful probability to firm security
Reverse Deception: prepared Cyber hazard Counter-Exploitation explains the best way to establish complicated power threats (APTs), categorize them in accordance with chance point, and prioritize your activities for that reason through utilizing specialist, field-tested deepest- and government-sector tools (NSA, FBI, and DOD).
APTs can't be obvious, unfold invisibly, after which proceed to dwell in an firm community, undetected. during this different ebook, the authors clarify how you can get—and stay—ahead of today's well-organized and very continual model of community enemies. The booklet describes the features of malware and botnets, how they could morph, avert detection, and spin off decoys that stay in-network, whereas showing to were wiped clean up and debugged. This exact consultant then finds the right way to observe the looks of malicious code, decode the categories of enemies they originate from, and eventually, how one can extricate malcode and deflect its destiny access into networks.
Reverse Deception: prepared Cyber probability Counter-Exploitation features:
> complete assurance of the number 1 feared kind of community assault at the present time, the APT
> Descriptions of cyber espionage strategies obvious within the U. S. and across the world, with comparisons of the categories of countermeasures permissible by means of legislation within the U. S. and Asia as opposed to much less strict international locations in Europe, the center East, and Africa
> captivating case stories and precise tales from the authors' FBI, DOD, NSA, and personal area work
> Foreword by means of Fred Feer, a safety expert with forty years' event with the U. S. military counterintelligence, CIA, RAND, and self sufficient consulting
> entire insurance of key facets of deception, counter-deception, behavioral profiling, and safeguard in the cyber realm
> Cat-and-mouse options from the easiest within the game—explains the best way to enforce deception and disinformation innovations opposed to numerous incoming threats geared toward engaging adversaries out into the open
> A clean standpoint on leading edge, field-tested rules for effectively countering present electronic threats—plus anticipated features of the following threats to come
> felony causes of services, obstacles, and specifications for supporting legislation enforcement investigations
Coverage includes:
Deception all through background to this day; The functions & objectives of Cyber Counterintelligence; The Missions and results of legal Profiling; felony & moral elements of Deception; assault Tradecraft; Operational Deception; instruments, strategies & strategies; assault Attribution; Black Hat Motivators; realizing complicated chronic Threats; whilst & whilst to not Act; Implementation & Validation strategies
“Each of those little books is witty and dramatic and creates a feeling of time, position, and personality. .. .I can't reflect on a greater method to introduce oneself and one’s pals to Western civilization. ”—Katherine A. Powers, Boston Globe. “Well-written, transparent and trained, they've got a breezy wit approximately them.
Translated by way of John & Charlotte Stanley.
With a Foreword through Robert A. Nisbet & an advent by means of Joh Stanley
It is a excitement to welcome this booklet into the English language, the extra so for the final excellence of the interpretation and for the precious advent that Professor Stanley has given to Sorel's paintings. This Frenchman has been in a position to divulge to the very center the fashionable thought of growth, the concept that mankind has improved in linear type some time past, is now progressing, and should proceed to growth indefinitely into the longer term, got here into being within the French Enlightenment.
- The Online Identity Theft Prevention Kit: Stop Scammers, Hackers and Identity Thieves from Ruining Your Life
- Running Like a Girl: Notes on Learning to Run
- Fooled by Randomness
- Let's Learn Japanese Picture Dictionary
- Extreme Alpinism: Climbing Light, Fast, and High
- Australia Day Regatta
Extra resources for The Man Who Loved Only Numbers: The Story of Paul Erdos and the Search for Mathematical Truth
Example text
It is accordingly less costly to society to have production carried out by one firm than by many. Thus, rather than have three railway or electricity companies laying separate networks of rails or cables where one would do, it may be more efficient to give one firm a monopoly subject to regulation of such matters as prices and access to the network. Determining whether a natural monopoly exists requires a comparison of demand for the product with the extent of the economies of scale available in production.
For other definitions of good or better regulation see Mandelkern Group on Better Regulation, Final Report (Brussels, 13 Nov. 2002) (‘Mandelkern Report’). 10 If Parliament is yet to provide a mandate because no regulatory statute has been passed in an area— say, when a regulatory Bill is being debated—any discussion of ‘good’ regulation is more open-ended than usual. Reference, in such circumstances, is likely to be made to the four criteria other than the mandate that are discussed here and also to governmental claims to possess a mandate for a certain regulatory approach (based, for instance, on manifesto statements) and to more general arguments concerning social justice.
Veljanovski, ‘Regulation by Cost Benefit Analysis’ (1984) 62 Public Administration 51. 23 See Prosser, Law and the Regulators, 15–24; ‘Regulation and Social Solidarity’ (2006) 33 Journal of Law and Society 364–87. 24 C. Foster, Privatisation, Public Ownership and the Regulation of Natural Monopoly (Oxford, 1992), ch. 9. 25 Prosser, Law and the Regulators, 24. See also Chapter 2, above, on rationales for regulating and Chapter 15, below, on the application of cost-benefit testing to regulation. 32 FUNDAMENTALS The Role of the Five Criteria The above five claims, it can be seen, are all fraught with difficulties but collectively they constitute a set of benchmarks for assessing regulatory regimes.



